Quantum computers are edging close to the muscle required to crack RSA and elliptic-curve keys that protect almost everything online. Waiting for “Q-day” invites attackers to harvest traffic now and decrypt it later. Governments have noticed, regulators are drafting timelines, and Cloudflare already flipped the switch—since October 2025, hybrid X25519 + Kyber secures more than 50 percent of its human-initiated traffic.
Where should you, the developer, start? This guide compares seven battle-tested options—from a one-click browser check to production-grade TLS libraries—using the metrics that matter: integration effort, performance hit, security maturity and licence flexibility. By the end, you’ll know which tool to try first and how to turn quick experiments into a confident post-quantum roadmap.
Ready? Let’s dive in and future-proof your crypto.
How the Tools Were Compared
The evaluation started with one question for every candidate: “Would a busy software team trust this in a real migration pilot?” If the answer was yes, the tool stayed on the list.
The breadth of algorithms was then examined. A library that only ships Kyber delivers speed, but it leaves you exposed if that scheme falters.
Integration effort was weighed. You do not have weeks to patch build systems, so anything that drops into an existing stack with minimal changes was favoured.
Performance followed close behind. Benchmarks had to show acceptable handshake latency, modest memory use, and solid throughput under load. Numbers beat anecdotes.
For security maturity, track records, audits, real-world deployments, and maintainer responsiveness were checked.
Finally, licensing and support were considered. Open source trims cost, yet commercial backing can save the day when deadlines loom.
Integration and performance counted slightly more than the other factors because a feature-rich library is pointless if it slows your API or takes a sprint to compile.
With the scorecard settled, hands-on testing began. Next, the first tool on the list.
Project Eleven browser check: instant client-side litmus test
Before tinkering with servers or libraries, it is essential to confirm whether browsers speak post-quantum. Project Eleven’s free browser check does exactly that.
Open the page; it launches a real TLS 1.3 handshake and returns a verdict in about two seconds: Hybrid X25519 + Kyber enabled or Classical only. No install, no command line.
The tool gives perspective. Developers often patch back ends, yet a server upgrade is worthless if Chrome or Firefox falls back to legacy curves. Seeing the test fail on your everyday browser is a visceral reminder that the ecosystem remains only half ready.
Under the hood, the checker scans the ClientHello and ServerHello messages for draft hybrid groups. If the cipher suite matches, you get a green light; otherwise, it explains the gap and links to the relevant experimental flag. Project Eleven’s quantum safe internet browser guide publishes the full list of identifiers the script looks for—today that includes hybrid groups X25519 + ML-KEM-768 (0xfe30) and secp256r1 + ML-KEM-768 (0xfe34) as well as the bare ML-KEM-512, 768, and 1024 codes—so teams know exactly what their ClientHello must advertise before wiring the check into CI.
It does not compile into your app or secure a tunnel, and that is fine. Treat it like a pocket flashlight: quick, bright, perfect for scouting the path before the team marches forward.
Run it at the start of any workshop, demo, or executive briefing. The red Not quantum-safe label sparks questions, sets stakes, and primes everyone for the deeper tools that follow.
Open Quantum Safe: the Swiss-army knife for early prototyping
When you want to explore every post-quantum algorithm in one place, Open Quantum Safe is the sandbox of choice.
At its core sits liboqs, a lean C library that bundles Kyber, Dilithium, SPHINCS+, Frodo, BIKE, Classic McEliece and many more KEM or signature schemes behind one consistent API.
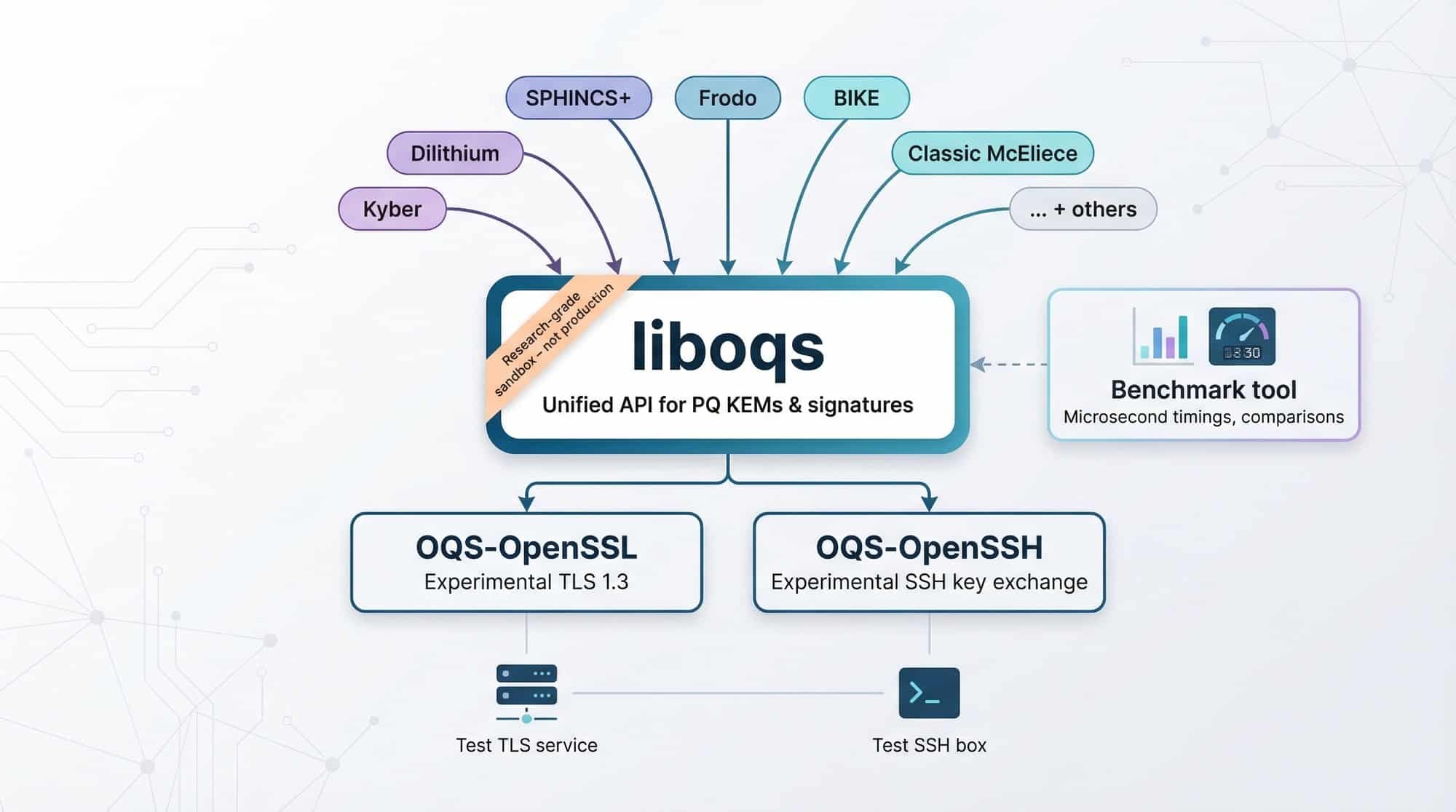
Pair liboqs with the OQS-flavoured OpenSSL build and those exotic ciphers appear beside AES and X25519. Patch OpenSSH with the companion fork and your next ssh to a test box can negotiate a Kyber key exchange. Flipping a feature flag suddenly feels like stepping ten years into the future.
Setup takes about an hour. Clone the repo, run cmake, compile, then point your app at the fresh libcrypto.so. The documentation is clear and the scripts behave, so you spend time testing rather than debugging.
Why invest in this experimental stack? Because it delivers answers fast. The built-in benchmark tool prints microsecond timings that reveal how Kyber flies while Frodo crawls. Swap algorithms in a single line of code, rerun the test, and hand stakeholders concrete numbers instead of guesses.
Remember, OQS calls itself research grade for a reason. Constant-time guards and side-channel hardening remain in progress. Treat the library as a proving ground, not a production shield.
As a proving ground, though, it shines. You can stand up a quantum-safe TLS service in a morning, demo it after lunch, and walk into sprint planning armed with real data, not speculation.
OpenSSL 3.5: mainstream TLS goes quantum ready
When OpenSSL moves, the industry follows. Version 3.5, released in April 2025, ships three new NIST selections directly in the core: ML-KEM (Kyber) for key exchange plus ML-DSA (Dilithium) and SLH-DSA (SPHINCS+) for signatures.
A routine apt update now becomes a post-quantum rollout plan; no forks, no fringe patches, same library you already trust.

From a developer’s seat the change feels anticlimactic. Recompile your app, add TLS_AES_256_GCM_SHA384:HYBRID_X25519_KYBER_LEVEL1 to the cipher string, and the handshake completes. No API gymnastics, no header rewrites.
Performance data calms skeptics. Kyber’s math is swift, so a hybrid X25519 + Kyber handshake adds a few microseconds and about 1 KB of traffic. Dilithium signatures verify faster than RSA-4096, while SPHINCS+ stays reserved for long-lived artifacts where size matters less than compromise.
Security audits never stop. OpenSSL’s vast user base puts fresh eyes on the code every day. Enterprise distros are already backporting the PQC modules, and FIPS validation sits on the roadmap once NIST finalises algorithm profiles.
Bottom line: if your service already runs OpenSSL, 3.5 is the friction-free path into the quantum-safe club. Upgrade a staging box this week, enable the hybrid suites, and watch packets flow as usual—only now they keep their secrets from tomorrow’s computers.
AWS s2n: cloud-grade speed with a quantum shield
Some teams value raw performance over a wide algorithm menu. s2n-TLS and its sibling s2n-QUIC answer that need.
Both default to a hybrid key exchange that pairs X25519 with Kyber Level 1, and AWS load tests show the switch trims peak connections per second by only eight percent while keeping latency nearly flat.
The small hit comes from efficient engineering. s2n is a slim C codebase focused on TLS 1.3 and QUIC, free of legacy branches. Tight inner loops simplify formal verification, and the AWS cryptography team runs those proofs on the handshake logic.
Integration feels natural if you already build on AWS. Many managed services speak TLS through s2n behind the scenes, so when Amazon enables PQC you inherit the upgrade automatically. For custom workloads, add the library as a pkg-config dependency, call the concise API, and let s2n negotiate the hybrid suite.
There is one compromise: algorithm choice. s2n ships only Kyber, betting on NIST’s primary KEM. Teams that require McEliece or Falcon need another library. If you want fast TLS and QUIC today, with a quantum-safe layer and single-digit latency impact, s2n offers a production-ready path.
wolfSSL: lean, mean, and ready for embedded machines
Routers, drones, and IoT sensors live on kilobytes, not gigabytes. That is wolfSSL’s territory. The library packs a full TLS 1.3 stack plus Kyber and Dilithium into a footprint small enough to sit beside a bootloader.

Add the build flag –enable-pqc and your firmware speaks the same hybrid handshake used in NSA CNSA 2.0 guidance. Because the core team owns the codebase end to end, they tune assembly for ARM and RISC-V, trimming cycles until a Kyber exchange feels no heavier than classic ECDH.
Commercial support is a key advantage. Hardware that ships for a decade cannot rely on community forums for patches. A paid licence delivers SLA-backed fixes and a FIPS validation path once NIST finalises module tests.
Algorithm variety is narrower than Open Quantum Safe, and GPL clauses may add cost. Even so, for teams that need post-quantum TLS in products with strict memory ceilings, wolfSSL stands out as the practical, certifiable choice.
Microsoft PQCrypto-VPN: kick the tires on a quantum-safe tunnel
Securing a website is one challenge, but protecting the pipes between data centres is another. Microsoft Research’s fork of OpenVPN lets you test post-quantum crypto across a full tunnel without touching application code.
Installation is straightforward: download the custom client and server binaries, set ecdh-curve frodo-1344 (or another supported KEM) in the config, and bring up the tunnel.
As soon as the banner appears, packets travel over a post-quantum key exchange.
The payoff is experiential data. Stream a 4K video, run iperf, or replicate a database. Large Frodo ciphertexts will tax the CPU, while hybrid modes glide. Hard numbers calm stakeholders faster than any slide deck.
This remains a lab tool. The repository carries a clear “research only” label and trails mainline OpenVPN security fixes. Use it like a crash-test dummy that shows how seat belts deploy, not the sedan you drive daily.
For teams planning site-to-site VPN upgrades, PQCrypto-VPN fills a crucial gap. It converts abstract crypto debates into dashboards of throughput, latency, and CPU graphs you can paste directly into a migration report.
Crypto-agility toolkits: map your crypto before you rip and replace
Libraries answer how. First, you must answer where. Ask any enterprise architect for a complete list of RSA-2048 keys in production, and the room goes quiet. That discovery gap is why platforms such as SandboxAQ Analyzer and Keyfactor AgileScan land on procurement shortlists.
These scanners crawl source repos, binaries, certificate stores, even running processes, then produce a cryptographic bill of materials. You see at a glance that the payment gateway still hard-codes SHA-1, the legacy API uses 1024-bit DH, and half your IoT fleet cannot accept keys larger than 1 KB.
Dashboards score each finding for quantum risk and swap effort. A green bar means you can drop in Dilithium with a config change; red flags hand-rolled crypto hidden in firmware. This triage prevents migration projects from turning into boil-the-ocean quests.

Reports export directly into ticket systems, turning abstract audits into sprint-ready tasks. Developers patch easy items now, security teams schedule firmware updates for devices in the field, and leadership tracks progress through weekly risk burn-down charts.
Most platforms carry enterprise pricing and a learning curve, yet skipping this step leaves blind spots that can derail a quantum-safe launch months later.
Conclusion
The seven tools in this guide cover the full arc of a post-quantum migration—from a two-second browser check that proves the gap exists, through research-grade libraries that let you benchmark every NIST candidate, to production TLS stacks and VPN tunnels that carry real traffic under hybrid encryption. No single tool handles every stage, but together they remove the guesswork that stalls most teams before they write a line of code.
Start where the friction is lowest. Run the Project Eleven browser check in your next team meeting to make the threat tangible, then stand up an Open Quantum Safe instance to collect hard performance numbers. When those numbers look solid, upgrade a staging box to OpenSSL 3.5 or s2n and let hybrid suites protect actual requests. Use a crypto-agility scanner to map every classical key still hiding in production so nothing slips through when the full rollout begins.
The quantum timeline is compressing. Cloudflare, AWS, and major browser vendors are already shipping post-quantum defaults, which means the ecosystem will not wait for stragglers. Testing today is cheap; retrofitting after a harvest-now-decrypt-later attack is not. Pick one tool from this list, run it before the week ends, and turn curiosity into a concrete migration plan.
