Teams are scrambling to fix security gaps after hackers found a way to use Trivy—a popular scanning tool—against the very people it was meant to protect. This supply-chain attack turned simple checks into a way for thieves to steal digital keys. A standard security check became a credential-stealing pathway, forcing teams to confront a reality where Trivy scanner compromises in ongoing supply chain attacks mean that automated pipeline secrets are likely already in adversary hands. Action must be immediate to stop lateral movement across cloud environments.
Keeping your software safe means trusting the tools you use, but this breach proves that even a trusted scanner can be turned into a back door for attackers. Protecting the software supply chain requires more than just running a scan; it demands a shift in how we handle build-runner environment variables and long-lived tokens. If a scanner holds the keys to your production environment, the blast radius of a single tag swap can dismantle your entire security posture in minutes.

Essential Facts: Trivy Supply Chain Breach and Secret Rotation
Someone swapped a safe security check for a fake one right under the nose of build systems. This trick turned a regular update into a massive leak of private passwords and access codes. Treat these next checks as an incident response drill—time is your most critical clue.
- Incident Window: The main exposure period centres on March 19–23, 2026, and the GHSA-69fq-xp46-6×23 vulnerability exposure windows provide the exact time-bounded map needed for log review and remediation.
- Attack Vector: A core tactic involved moving GitHub Actions tags to malicious commits, a method documented in StepSecurity’s confirmed tag and release timeline that can leave workflow files looking unchanged.
- Confirmed Identifier: The incident is tracked as CVE-2026-33634, and the CVE-2026-33634 affected component summary clarifies what was targeted and why partial rotation fails to evict attackers.
- Immediate Risk: Any credentials accessible to a build runner, such as GitHub tokens, cloud keys, container registry logins, and Kubernetes tokens, should be treated as potentially exposed, echoing the reset-first guidance in a Canadian government advisory on the Trivy incident.
- Fast Reality Check: If the pipeline can deploy, push images, or touch production namespaces, assume the scanner step could see the same permissions and reduce that blast radius now.
Response teams started noticing a pattern: the scanner would give a thumbs-up, but someone was copying the keys behind the scenes while everything looked normal. The key ring may have been copied while everything looked normal.

Analysing the Trivy Supply Chain Attack on CI/CD Infrastructure
Mechanics of the Compromise and Critical Risks
Hackers love automated tools because they move so fast. When a trusted piece of software gets replaced with a fake, the system just keeps running and carries the attacker right into the heart of the network. forced tag swaps on GitHub advisories prove how this blast radius expands far beyond a single tool install.
The breach hinged on release plumbing that many teams treat as stable, a point documented in maintainer-side Trivy supply chain attack insights that explains why secret rotation is treated as the first move rather than a clean-up task.
Scanner proximity to sensitive data drastically expands the attack surface, elevating this compromise beyond the risks of a typical software vulnerability. Standard delivery pipelines often prioritise speed over safety. This creates a few specific risks:
- Routine releases might skip manual checks to save time.
- Automated push permissions give the system too much power.
- Attackers can hide inside the very tools meant to speed things up.
Role of Trivy in Pipeline Vulnerability Management
Trivy is an open-source tool used to scan container images, file systems, and Kubernetes configurations for vulnerabilities. The Trivy vulnerability scanner project operates across containers, code repositories, and Kubernetes clusters. DevSecOps teams integrate Trivy into CI/CD pipelines to automate security scans before code reaches production.
Placement matters. Scanners run in environments that read build-time secrets or cloud credentials. If one digital key is stolen, attackers can use it to jump from one service to another. This turns a single leak into a total security failure across all your cloud systems. This pattern highlights multi-cloud vulnerability management risks common in modern environments where scan steps inherit excessive deployment-level permissions. Scan steps often share the same access levels as deployment steps, creating a convenience that doubles as a security liability.

Understanding the Supply Chain Attack Vector and Malware Objectives
Exploiting Tag Mutability for Silent Malware Delivery
Tag mutability provides the primary vector for silent compromise. Referencing GitHub Actions by tag creates a false sense of version stability until force-pushed commits redirect pipelines to malicious code. Detailed GitHub Actions tag hijack analysis confirms that workflows remain visually identical while executing compromised logic.
Workflow risks escalate for teams pulling scanners from registries by default.
Minor tag updates can trigger silent data exfiltration without altering the visible commit history of the workflow. Following Docker Hub supply chain compromise guidance that treats digest pinning as a non-negotiable first-response move stops these “scan then leak” habits before they ship.
Identifying Malware Targets and Credential Exfiltration Pathways
Malware transforms vulnerability scanners into exfiltration tools by harvesting secrets from build runners. This incident represents a critical credential exposure event rather than a minor software error. Attackers don’t just stop after one scan. They reuse stolen cloud keys days later to push bad code or quietly steal production data when no one is looking.
Finding where the hackers went requires looking for small clues left behind in your system logs after the attack happened, leveraging Microsoft’s investigation into the Trivy compromise as a roadmap for build runner security. Broad permissions allow attackers to replay access using short-lived tokens and build-time variables.
CI/CD Incident Response Checklist and Pipeline Security Hardening
Immediate Steps for Breach Containment and Remediation
Immediate action stops attackers from reusing stolen secrets. Revoke exposed credentials and restrict future access now. Leaked tokens become late-night production changes that nobody intended if a build runner has permission to deploy.
Standardised cybersecurity breach containment measures prioritise revoking exposed credentials. This approach is consistent with Wiz’s CI/CD environment triage protocols that help teams confirm execution windows and rotate secrets across repositories.
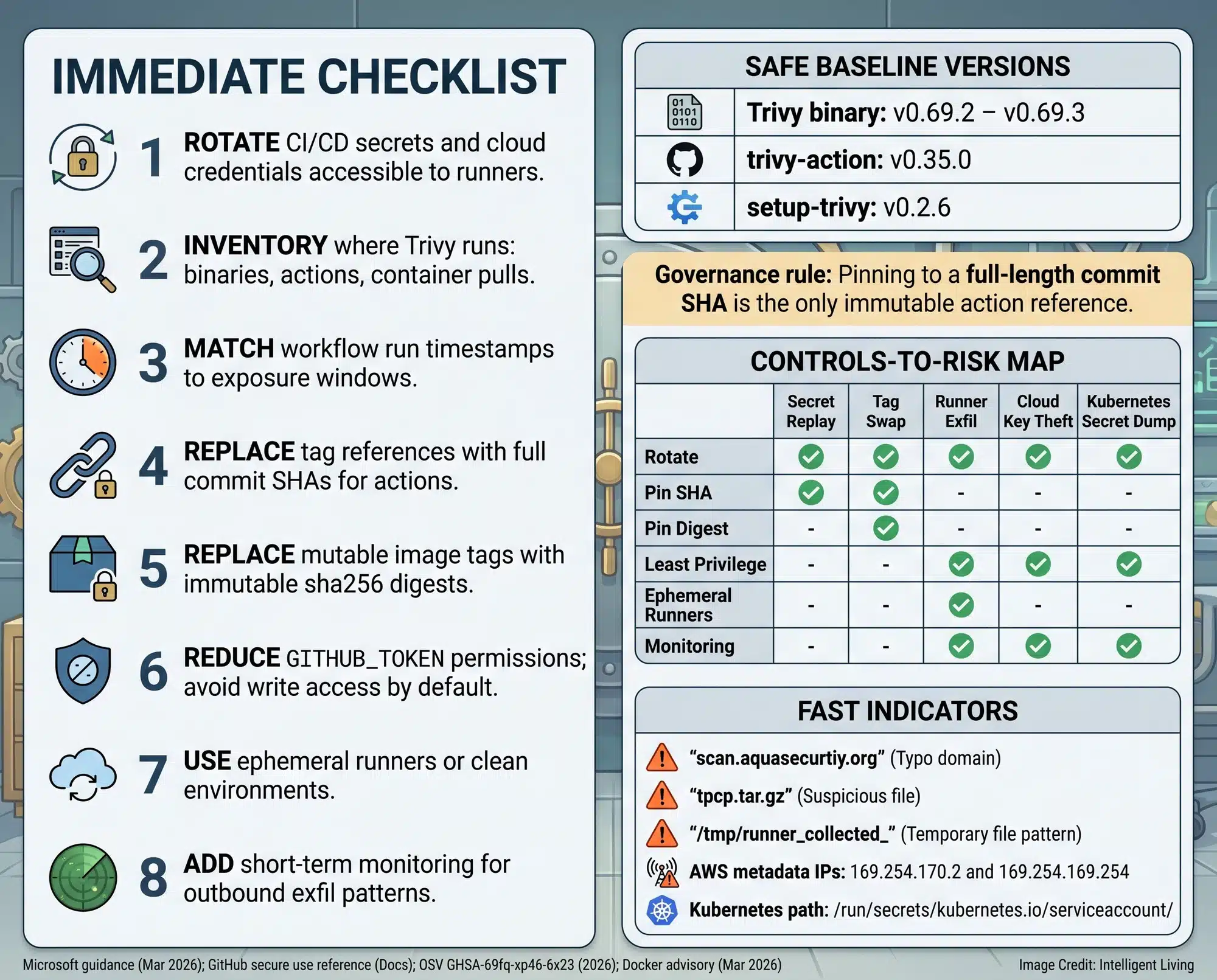
- Rotate Secrets Atomically: Replace API keys, deployment tokens, registry passwords, and cloud credentials immediately so old credentials are invalidated.
- Audit Pipeline Runs: Review logs for unusual outbound connections or unexpected repo activity during the exposure window.
- Pin What Executes: Enforce GitHub Actions secure-use hardening policies to replace mutable tags with immutable commit SHAs.
- Reduce Runner Permissions: Apply least-privilege and remove long-lived credentials from CI.
- Increase Monitoring Temporarily: Add alerting for new tokens or unfamiliar IP access to cloud consoles.
5 Shifts in Modern Software Supply Chain Security
- Version Labels Stop Feeling Safe: Simple version labels aren’t safe enough anymore. Using permanent ‘digital fingerprints’ is now the only way to be sure you’re running the right code.
- Security Tools Become Privileged Apps: Scanners require strict boundaries because they see everything they scan.
- Secrets Rotation Becomes a Routine Drill: Credential hygiene shifts from a quarterly chore to an always-ready muscle.
- Provenance Becomes a Real Operational Policy: Verifying who built an artefact and from what code becomes a top priority.
- Incident Response Leans on Automation: Relying on automated incident response frameworks shrinks cleanup time when pipeline leaks occur.

Real-World Impact and New Protocols for Pipeline Trust
Evidence-Based Risks of CI/CD Supply Chain Attacks
Breach attribution from CERT-EU confirms that a European Commission cloud compromise originated from the Trivy supply chain breach. The CERT-EU European Commission breach assessment confirms that short-term exposure windows create persistent downstream data risks.
Documented Cases of Unauthorised Environment Access
It doesn’t matter who got hit first; what matters is how it happened. A stolen password from a build system can be used weeks later, long after everyone thinks the danger has passed. Responders treat rotation like turning off a gas valve to stop replay even if an attacker copied the key.
Why Supply-Chain Incidents Keep Echoing for Weeks
Supply-chain compromises create delayed risk as leaked credentials touch multiple systems. A registry token can push a container image that a trusted cluster then pulls automatically. Shortening credential lifetimes narrows where secrets are available.

Securing Software Supply Chains Through Secret Rotation and Immutable SHA Pins
Keeping your software safe isn’t something you do just once. It takes a plan to keep checking, rotating keys, and staying one step ahead of the next trick. Simple mistakes leading to data breaches, such as leaving over-broad tokens in build variables, create unnecessary risk for teams of any size.
Building resilience depends on assuming total compromise and maintaining incident response readiness. Organisations face cybersecurity compliance challenges during incidents where cleanup time exceeds expectations. Pushing a poisoned image is easy for an adversary when registries trust every request by default.
Frequently Asked Questions about the Trivy Attack and CI/CD Security
How Do I Know if My CI/CD Secrets were Stolen?
Check your job logs for unexpected outbound connections and review cloud audit logs for unusual token use. Inspect registries for surprise image pushes or unfamiliar automation accounts created during the March exposure window.
Why is Rotating API Keys Better than Just Patching Trivy?
Patching the tool stops new infections, but it does not stop attackers from using keys they already copied. Rotating API keys and registry passwords invalidates stolen credentials immediately, preventing future replay attacks.
What is the Safest Way to Reference GitHub Actions?
Reference a specific immutable commit SHA instead of a movable version tag. Pinned references ensure the exact code you vetted is what runs, preventing silent tag swaps from injecting malicious malware into your builds.
Can Attackers Use Stolen Build-Time Environment Variables Later?
Adversaries harvest these variables to gain persistent access to cloud consoles or private container registries. Stolen cloud keys allow attackers to create new access paths days after the initial scan compromise.
How Can I Reduce the Blast Radius of My Build Runners?
Apply strict least-privilege permissions and remove long-lived credentials from your pipeline settings. Utilising Docker image digests ensures a SHA-256 reference cannot be swapped, while navigating the challenges of vulnerability management helps teams separate real risk from noise.
